SAP Security - Table of Content
- What is SAP Security?
- SAP Security: How Does It Work?
- SAP Security Concepts
- How to Configure SAP Security?
- Conclusion:
What is SAP Security?
SAP Security is a delicate balancing act for preventing unauthorized use and access to SAP data and applications. SAP provides a variety of security tools, methods, and measures to safeguard these data. SAP security ensures that users can only utilize SAP functionality that is required for their work.
SAP systems store very sensitive and secret information about their customers and enterprises. As a result, an audit of an SAP computer system is required regularly to ensure its data integrity and security.
For example, a warehouse employee who is in charge of producing buy orders must not approve a valid purchase order; otherwise, he may produce and approve as many purchase orders as he wants.
In this situation, a higher authority should approve the purchase order, which is a normal security measure.
Following that, in this SAP Security for Beginners tutorial, we'll go through various SAP Security principles.
What Is the Importance of SAP Security?
Large volumes of secret or sensitive data are stored in SAP systems. Users on your network who use an SAP system should have access to everything they need to execute their duties, but not too sensitive data like confidential information or financial records. If an employee gains unintended access to data that must be protected, they risk causing difficulties by deleting or transferring something. Even worse, someone accessing sensitive data on purpose, whether to harm your organization, data leakage, or commit fraud, is a terrifying prospect. Furthermore, certain types of information must be properly protected in specific businesses (such as those financial data or involving health) for regulatory reasons.
Become a SAP Security Certified professional by learning this HKR SAP Security Training !
SAP Security: How Does It Work?
SAP ERP includes software for human resources, accounting, finance, sales, goods and services, manufacturing, and logistics, among other things. All businesses require networked systems with the capacity to transfer data between different portions of the company as needed. ERP systems combine back-office and front-office tasks, including stock management, data analysis, organizational planning, and governance planning, as well as customer relationship management (CRM) and e-business.
ERP is made up of several applications, including those for human resources, accounting, CRM, and sales, among others. You could save time and money by combining these processes and centralizing their management.
Once the SAP system is configured, SAP security is in place to ensure that the system functions as intended, with no security or data access issues. SAP security is divided into three categories:
- Confidentiality: This implies that no information should be shared without authorization.
- Integrity: No data must be altered without authorization.
- Availability: DDoS (distributed denial-of-service) attacks must be prevented.

SAP Security Training
- Master Your Craft
- Lifetime LMS & Faculty Access
- 24/7 online expert support
- Real-world & Project Based Learning
SAP Security Concepts
Below are the main Security Concepts in SAP:
1. STAD Data
The front door to SAP's capabilities is through transaction codes. Using STAD data, you can protect yourself against unwanted transaction access. Is there a record of who accessed what functions? And when? The security concept could be monitored, analyzed, audited, and maintained using STAD data.
2. Cryptographic library from SAP
SAP's default encryption offering is the SAP Cryptographic Library. It's used to connect multiple SAP server components via Secure Network Communication (SNC). You must purchase an SNC-certified partner product for front-end components.
3. Security of the Internet Transaction Server (ITS)
A middleware component called Internet Transaction Server (ITS) is used to make SAP system applications accessible via a web browser. Many security features are incorporated into the ITS design, such as the ability to run the Agate and Wgate on distinct hosts.
4. Basics of Network (Network Ports, DMZ, and Firewalls, SAPRouter)
Firewalls and DMZ, Network Ports, SAPRouter, and other basic security tools are used by SAP. A firewall is a hardware and software device that defines the connections that should be established between communication partners. Application-level gateways such as SAPRouter and SAP Web dispatcher can be used to filter SAP network traffic.
5. Web-AS Security (Enterprise Portal Security, SSL, Load Balancing)
SSL (Secure Sockets Layer) is a standard security technique that allows a server and a client to establish an encrypted connection. By selecting the encryption variables, you can authenticate the communication parties (server and client) with SSL.
Both partners have authenticated via sap cyber security. Data sent between the server and the client will be safeguarded, allowing any data tampering to be detected. Furthermore, all data sent between the client and the server is encrypted. Following the guidelines in the enterprise portal, a security guide could help safeguard the system.
6. Single Sign-On
You can use the SAP single sign-on capability to configure the same user credentials for numerous SAP platforms. It aids in the reduction of administrative costs and security risks connected with multiple user credentials. During data transfer, it protects confidentiality by encrypting the data.
7. AIS (Audit Information System)
The Audit Information System (AIS) is an auditing tool that you may use to thoroughly examine the security aspects of your SAP system. AIS is a software program for conducting system and business audits. The Audit InfoStructure is where AI displays its data.
We'll learn about SAP security for mobile apps next in this SAP Security tutorial.
Become a SAP Certified professional by learning this HKR SAP Training in Hyderabad !

Subscribe to our YouTube channel to get new updates..!
Mobile SAP Apps SAP Security
With a rise in mobile users, SAP apps are now available on mobile. However, this exposure poses a risk. The most serious hazard to an SAP app is the possibility of a customer's sensitive data being lost by an employee.
The benefit of mobile SAP is that the majority of mobile devices have remote wipe capabilities. Many of the CRM-related features that businesses are aiming to mobilize are cloud-based, which means that confidential data is not stored on the device.
SAP Mobile Academy, SAP Hana cloud, SAP Afaria, and SAP Netweaver Gateway are some of the most prominent mobile SAP security suppliers.
Following that, we'll learn about SAP security best practices in this SAP Security for Beginners tutorial.
Top 30 frequently asked SAP Security Interview Questions !
How to Configure SAP Security?
Access to both application and database servers must be restricted while utilizing SAP systems. To prevent unauthorized access to data, user accounts in an SAP system should be properly specified as roles with certain rights (or lack thereof). This safeguards the system as a whole from damage or data loss by preventing unauthorized data loss.
Using a firewall, regulating access, encrypting data, and using digital certificates, as well as antivirus and security management software, security should be dispersed over several layers and components of the system. With that in mind, these are the most important stages in securing your SAP system:
Align Settings
SAP security settings should be in line with company standards regarding who has access to what data and what data has to be safeguarded or considered confidential. You should also make sure that your company follows basic security measures, such as mandating users to use passwords that are at least a certain length or combination of characters, and restricting access to a system or database after a certain number of failed password tries.
Make sure you know who has sensitive roles in your organization because the most powerful roles (those with the most access) are also the most hazardous.
Make an emergency procedure
If an SAP security issue emerges, network administrators must have the necessary permissions to change and remove privileges from other SAP system users. The SAP security process must be managed by network administrators, and everything must be pre-established and set up so that they can respond swiftly in the case of an incident.
Review and housekeeping
Keep track of who has access to which data, when they have access, where they have access, and why. You should maintain this list updated regularly several times as part of good housekeeping. Security access lists can easily become out of date when people shift jobs within an organization or when new people join.
Security Tools
Using security technologies that monitor SAP access can help you more easily identify any vulnerabilities or gaps in your processes, lowering the chance of an internal assault or data breach. Your IT team will be able to focus on other responsibilities as a result of this.
You may use a variety of tools to help you set up SAP security, including access management software and other types of security technologies.
1. Access Rights Manager
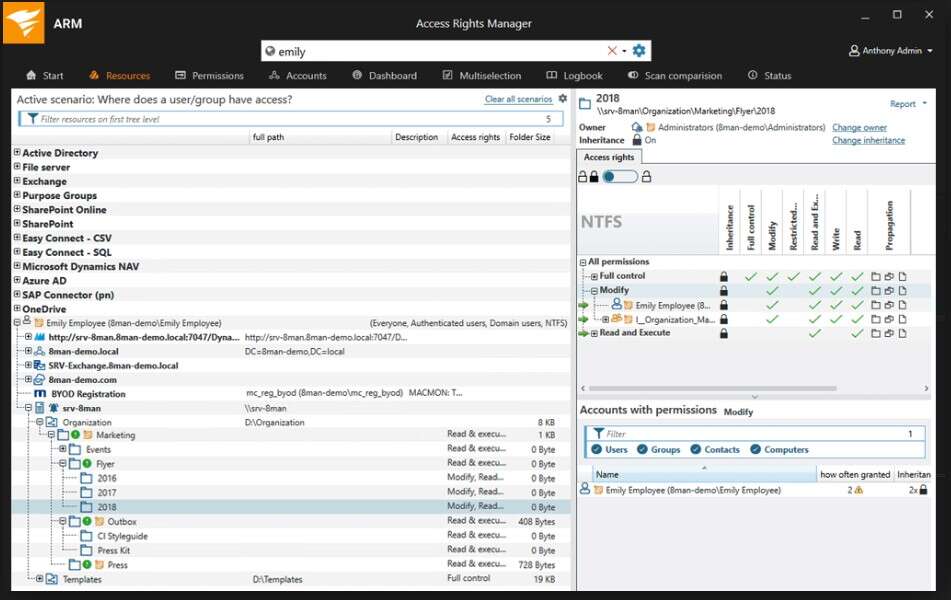
The SolarWinds Access Rights Manager is the solution I recommend for managing access security (ARM). SAP R/3 is now supported by ARM as well. This allows you to look for security-critical transaction codes while also recognizing numerous authorizations at the same time. Through the ARM interface, you can also view which Active Directory users are allocated to each SAP account, and you may add, edit, or delete user access to different files or types of data as needed.
An ARM can keep track of potentially unauthorized users as well as malicious or inadvertent data destruction by monitoring and auditing changes to both Group Policy and Active Directory. The alerting system is also effective, and it can instantly detect unexpected file and permission changes, allowing the network administrator to swiftly identify a potential problem.ARM allows IT workers to virtually automate the task of access rights management and provide auditor-ready user access reports for compliance purposes, saving them a significant amount of time. Overall, it's simple to use and a good all-around tool for keeping your company informed about internal security threats.
2. Access Control Suite for SAP Symmetry
To avoid compliance failures and illegal data breaches, the Symmetry Access Control Suite analyses SAP risks and identifies sensitive data. It also makes it simple to resolve segregation of duties (SOD) problems and manage SAP software access. It provides SAP emergency access procedures as well as the ability to log and trace everything a user does throughout a session.
3. Netwrix Auditor
Whether sensitive or regulated information is housed on-premises or in the cloud, the Netwrix Auditor works to detect and classify it consistently and properly. It provides security intelligence, allowing you to keep track of who has access to what, as well as when and how people access data on your servers. It can also generate reports that comply with PCI DSS, HIPAA, SOX, GDPR, GLBA, FISMA/NIST, and CJIS security standards. You can either try the software for free or buy it on a per-user basis.
Solutions for SAP Security
While your internal IT team could handle SAP security processes, they may require additional training or assistance to manage all of the threats. One of the best ways is to outsource some of your SAP security monitoring to third-party security technology like Access Rights Manager, which you can sample for free for 30 days to evaluate if it fits your SAP security requirements.
A checklist of SAP Security Best Practices
- Network settings and Landscape architecture are assessed.
- Assessment of OS security during SAP deployment.
- Assessment of the database management system's security.
- Security assessment of SAP NetWeaver.
- Internal access control assessment.
- SAP components such as SAP Gateway, SAP Messenger Server, SAP Portal, SAP Router, and SAP GUI are assessed.
- Evaluation of change and transportation procedures.
- Compliance with DSAG, OWASP, SAP, and ISACA standards is assessed.
Conclusion:
SAP Security is defined as a balancing act that protects SAP data and applications from illegal access and use. We have successfully finished learning the SAP Security Concepts. The good news regarding SAP mobile app security is that most mobile devices include remote wipe capabilities. At last, we also have discussed the best SAP Security practices in this blog.
Related Articles:
About Author
Kavya works for HKR Trainings institute as a technical writer with diverse experience in many kinds of technology-related content development. She holds a graduate education in the Computer science and Engineering stream. She has cultivated strong technical skills from reading tech blogs and also doing a lot of research related to content. She manages to write great content in many fields like Programming & Frameworks, Enterprise Integration, Web Development, SAP, and Business Process Management (BPM). Connect her on LinkedIn and Twitter.
Upcoming SAP Security Training Online classes
| Batch starts on 29th May 2026 |
|
||
| Batch starts on 2nd Jun 2026 |
|
||
| Batch starts on 6th Jun 2026 |
|

